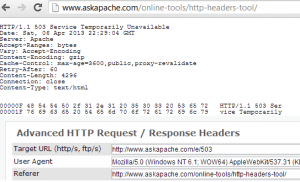
 This is a big update from the last time I looked into this, when I enumerated 57 Status Codes that Apache 2.x was capable of handling. This list contains 83 Status Codes recognized by Apache. I compiled the latest 2.4.4 Apache in order to view the actual codes sent by a live server.. very cool. You can read about the newest HTTP Status Codes in RFC 6585.
This is a big update from the last time I looked into this, when I enumerated 57 Status Codes that Apache 2.x was capable of handling. This list contains 83 Status Codes recognized by Apache. I compiled the latest 2.4.4 Apache in order to view the actual codes sent by a live server.. very cool. You can read about the newest HTTP Status Codes in RFC 6585.
Net Apache cURL ErrorDocument Htaccess HTTP HTTP Headers Redirect Status Code
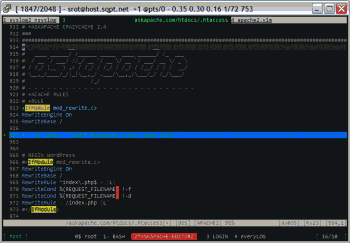
#### No https except to wp-admin -
# If the request is empty ( implies fopen or normal file access by a php script )
RewriteCond %{THE_REQUEST} ^$ [OR]
# OR if the request if for wp-admin or wp-login.php
RewriteCond %{REQUEST_URI} ^/(wp-admin|wp-login.php).*$ [NC,OR]
# OR if the Referer is https
RewriteCond %{HTTP_REFERER} ^https://www.askapache.com/.*$ [NC]
# THEN skip the following rule, basically all this does is force https or badhost to be redirected
# BUT because of the above 3 rewritecond's, this won't break poorly written admin scripts
RewriteRule .* - [S=1]
RewriteCond %{HTTPS} =on [OR]
RewriteCond %{HTTP_HOST} !^www.askapache.com$ [NC]
RewriteRule .* https://www.askapache.com%{REQUEST_URI} [R=301,L]
RewriteCond %{THE_REQUEST} ^[A-Z]{3,9} /(wp-admin/.*|wp-login.php.*) HTTP/ [NC]
RewriteCond %{HTTPS} !=on
RewriteRule .* https://%{SERVER_NAME}%{REQUEST_URI} [R=301,L] Htaccess RewriteCond RewriteEngine RewriteRule
 Ultimate Redirect Cheatsheet for multiple programming languages. Redirecting Users with Javascript redirect, meta refresh redirect, and php redirect, also htaccess methods, python, coldfusion, asp, perl, etc.
Ultimate Redirect Cheatsheet for multiple programming languages. Redirecting Users with Javascript redirect, meta refresh redirect, and php redirect, also htaccess methods, python, coldfusion, asp, perl, etc.
Htaccess 301 Htaccess Redirect URL redirection
 .htaccess is a very ancient configuration file for web servers, and is one of the most powerful configuration files most webmasters will ever come across. This htaccess guide shows off the very best of the best htaccess tricks and code snippets from hackers and server administrators.
.htaccess is a very ancient configuration file for web servers, and is one of the most powerful configuration files most webmasters will ever come across. This htaccess guide shows off the very best of the best htaccess tricks and code snippets from hackers and server administrators.
You've come to the right place if you are looking to acquire mad skills for using .htaccess files!
Apache, Hosting, Htaccess, Optimization, Security, SEO, Web Development, WordPress .htpasswd 301 Redirect Apache Apache HTTP Server Cache Hosting Htaccess Htaccess Software HTTP Headers httpd.conf HyperText Transfer Protocol mod_rewrite Redirect RewriteCond RewriteRule SSL
Using FastCGI on DreamHost and .htaccess
Shell Scripting
thought I'd take a break from coding and post about how open-source is such a great tool for finding the best answers to the toughest questions,
/** is the status code informational */
#define ap_is_HTTP_INFO(x) (((x) >= 100)&&((x) < 200))
/** is the status code OK ?*/
#define ap_is_HTTP_SUCCESS(x) (((x) >= 200)&&((x) < 300))
/** is the status code a redirect */
#define ap_is_HTTP_REDIRECT(x) (((x) >= 300)&&((x) < 400))
/** is the status code a error (client or server) */
#define ap_is_HTTP_ERROR(x) (((x) >= 400)&&((x) < 600))
/** is the status code a client error */
#define ap_is_HTTP_CLIENT_ERROR(x) (((x) >= 400)&&((x) < 500))
/** is the status code a server error */
#define ap_is_HTTP_SERVER_ERROR(x) (((x) >= 500)&&((x) < 600))
/** is the status code a (potentially) valid response code? */
#define ap_is_HTTP_VALID_RESPONSE(x) (((x) >= 100)&&((x) < 600))
Hacking
Apache, Hosting 2.4 Apache Error
2 awesome ways to implement caching on your website using Apache .htaccess or httpd.conf. Both methods are extremely simple to set up and will dramatically speed up your site! Htaccess Cache Cache-Control ETag Expires Header Headers Htaccess mod_expires mod_headers
SSLOptions +StrictRequire
SSLRequireSSL
SSLRequire %{HTTP_HOST} eq "google.com"
ErrorDocument 403 https://google.com
Some of the Ins and Outs of using SSL Connections with Apache.
Htaccess 301 Redirects Htaccess mod_rewrite SSL
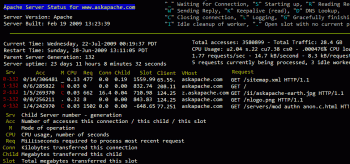
Learn how to setup, configure, secure, optimize, and create a low-maintenance website the AskApache way. I'm piecing together all the hacks, tricks, methods, and ideas discussed throughout this blog and all across Netdom and glueing them all together to show you how to have the most optimized, crazy fastest, and best website setup I can think of.
Hosting Apache HTTP Server Caching Htaccess HTTP linux operating systems round-robin DNS technology Web Developer Web server
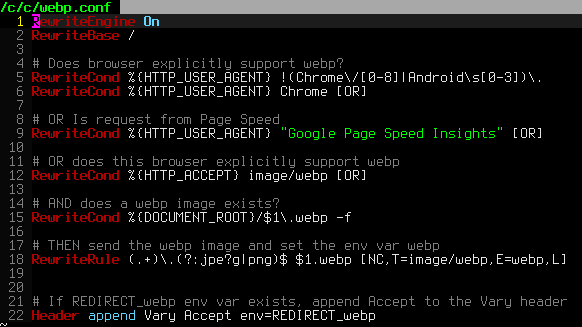
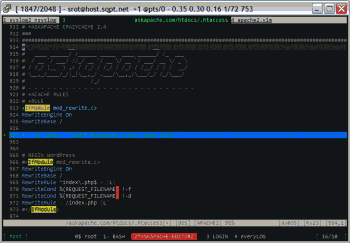
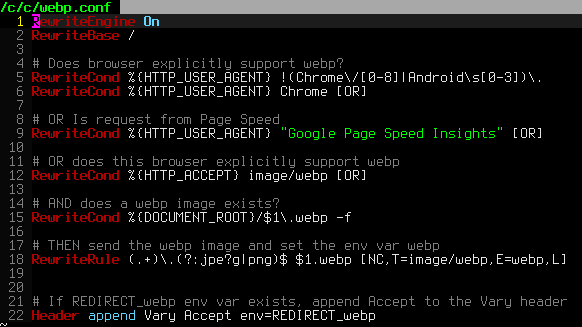
 htaccess rewrite Master Class! If you understand the basics of mod_rewrite, or if you literally write the mod_rewite.c code, this article will transform your thinking. The transformation is profound. Deeply effective. Culmination of the best of the best mod_rewrite tricks for understanding and learning exactly what rewrite is doing.
htaccess rewrite Master Class! If you understand the basics of mod_rewrite, or if you literally write the mod_rewite.c code, this article will transform your thinking. The transformation is profound. Deeply effective. Culmination of the best of the best mod_rewrite tricks for understanding and learning exactly what rewrite is doing.
Htaccess Htaccess mod_rewrite PHP RewriteCond RewriteRule
- When php run as Apache Module (mod_php)
- When php run as CGI
- When cgi?d php is run with wrapper (for FastCGI)
PHP CGI Htaccess PHP php.ini
Htaccess Apache HTTP Server Htaccess Redirect rewrite RewriteBase RewriteCond RewriteEngine RewriteLock RewriteLog RewriteMap RewriteOptions RewriteRule
 3-Part article covering practical implementation of 3 advanced .htaccess features. Discover an easy way to boost your SEO the AskApache way (focus on visitors), a tip you might keep and use for life. Get some cool security tricks to use against spammers, crackers, and other nefarious sorts. Take your site's error handling to the next level, enhanced ErrorDocuments that go beyond 404's.
3-Part article covering practical implementation of 3 advanced .htaccess features. Discover an easy way to boost your SEO the AskApache way (focus on visitors), a tip you might keep and use for life. Get some cool security tricks to use against spammers, crackers, and other nefarious sorts. Take your site's error handling to the next level, enhanced ErrorDocuments that go beyond 404's.
Htaccess SSI
 We've figured out what mod_rewrite variables look like, a cheatsheet of the actual value.
We've figured out what mod_rewrite variables look like, a cheatsheet of the actual value.
Htaccess Apache cheatsheet Htaccess htaccess file mod_rewrite PHP rewrite Rewriting
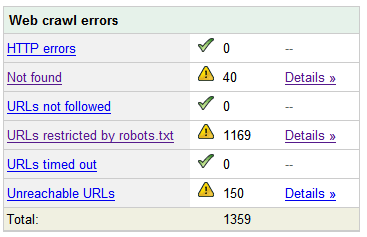
Learn how in a year, with no previous blogging experience this blog was able to rank so high in search engines and achieve 15,000 unique visitors every day. Uses combination of tricks and tips from throughout AskApache.com for Search Engine Optimization.
SEO
Comprehensive .htaccess example file with advanced examples in 1 htaccess sample skeleton .htaccess file with the very best apache htaccess examples... Updated frequently based on detailed info from the Apache htaccess tutorial.
Htaccess Allow AuthUserFile Deny Htaccess Redirect RewriteCond RewriteEngine RewriteRule
Apache Security tips and tricks for securing Apache Web Servers using htaccess, httpd.conf, and other built-in techniques to thwart attackers. This really should be required reading for any Apache admin or user because these little tricks are so easy to do.
Htaccess
 Here is even more information from the Ultimate Htaccess Part I. For now this is very rough and you will want to come back later to read it.
Here is even more information from the Ultimate Htaccess Part I. For now this is very rough and you will want to come back later to read it.
Htaccess Apache HTTP Server Htaccess World Wide Web
Htaccess
This is all new, experimental, and very very cool. It literally uses .htaccess techniques to create several virtual "locked gates" that require a specific key to unlock, in a specific order that cannot be bypassed. It uses whitelisting .htaccess tricks to specify exactly what is allowed, instead of trying to specify everything that isn't allowed. Also, by setting specific cookies/tokens after successfully passing through a gate, we can then require the exact cookie/token from the previous gate, which stops an attacker from skipping or bypassing gates.
Htaccess
How to password-protect, Allow or Deny a visitor based on a condition. If you are having trouble getting htaccess-based password protection to work see: Troubleshooting htaccess Authentication: Getting it to work
Htaccess AuthName AuthType FilesMatch Htaccess Password Password Protection Require
mod_rewrite is very useful in many situations. Yet some behaviors were not so obvious when I started to mess with it. After many testings, I understand it much better, now. Having said that, I do not pretend to know it perfectly. I also make mistakes.
Htaccess
If you examine the preferences dialog of any modern Web browser (like Internet Explorer, Safari or Mozilla), you'll probably notice a 'cache' setting. This lets you set aside a section of your computer's hard disk to store representations that you've seen, just for you. The browser cache works according to fairly simple rules. It will check to make sure that the representations are fresh, usually once a session (that is, the once in the current invocation of the browser).
Optimization
 So my blog as been rather quiet for almost a year now, and very few updates if any have been released for my Password Protection PLugin, my Google 404 Plugin, and definately not for my AskApache CrazyCache plugin, which I will be releasing last... So for all of you who've helped me out by sending me suggestions and notifying me of errors and sticking with it... Just wanted to say sorry about that, and thanks for all the great ideas.. Well, I've been sticking with it as well believe it our not. I manage to get free days once in a while, and then its time to jam.
So my blog as been rather quiet for almost a year now, and very few updates if any have been released for my Password Protection PLugin, my Google 404 Plugin, and definately not for my AskApache CrazyCache plugin, which I will be releasing last... So for all of you who've helped me out by sending me suggestions and notifying me of errors and sticking with it... Just wanted to say sorry about that, and thanks for all the great ideas.. Well, I've been sticking with it as well believe it our not. I manage to get free days once in a while, and then its time to jam.
WordPress Apache HTTP Server CGI Debugging HTTP protocol Htaccess SuexecUserGroup
Mod_Security rivals Mod_Rewrite in the amount of features it provides. I decided to go ahead and post what I learned about it today, even though its tough to give away such awesome htaccess and apache tricks.. Learn how to control spam once and for all, conditionally log/deny/allow/redirect requests based on IP, username, etc.. Mod_Security is so fine!
Htaccess Htaccess mod_security security
Links to htaccess tutorials and howtos in the htaccess forum
Htaccess
Server and Environment Variables are used by The Apache HTTP Server by provides a mechanism for storing information. This information can be used to control various operations such as logging or access control.
Htaccess
 Fresh .htaccess code for you! Check out the Cookie Manipulation and environment variable usage with mod_rewrite! I also included a couple Mod_Security .htaccess examples. Enjoy!
Fresh .htaccess code for you! Check out the Cookie Manipulation and environment variable usage with mod_rewrite! I also included a couple Mod_Security .htaccess examples. Enjoy!
Originally Posted: 3/29/2008
Htaccess
Very nice tutorial dealing with the robots.txt file. Shows examples for google and other search engines. Wordpress robots.txt and phpBB robots.txt sample files. SEO
A hit-list of some of my favorite mod_rewrite code snippets for .htaccess files
Htaccess
 Nifty SEO tip to get Search Engine Bots to check your site every hour until you finish working on it and tell them you are finished.
Nifty SEO tip to get Search Engine Bots to check your site every hour until you finish working on it and tell them you are finished.
SEO
 A plugin built to generate static files from php+mysql for Apache to serve the way its supposed to be.. My dream. Conclusion: Needs some improvement, pretty sweet though.
A plugin built to generate static files from php+mysql for Apache to serve the way its supposed to be.. My dream. Conclusion: Needs some improvement, pretty sweet though.
Optimization
Apache .htaccess Directives and Loaded Modules allowed on DreamHost Apache Server 2 Setups.
Hosting
 This article shows how to save and modify php session data, cookies, do anything really... without using ajax or iframes or forcing the user make a request.
This article shows how to save and modify php session data, cookies, do anything really... without using ajax or iframes or forcing the user make a request.
PHP
Grab the latest php.ini developmental version and discover new or previously hidden php runtime configuration settings... ahead of everyone else!
PHP
 Just a very brief look at speeding up form submission by delegating the processing and bandwidth to your server, not your client.
Just a very brief look at speeding up form submission by delegating the processing and bandwidth to your server, not your client.
PHP bottleneck cURL form fsockopen PHP snoopy
Htaccess
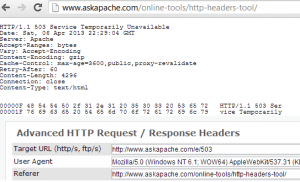 This is a big update from the last time I looked into this, when I enumerated 57 Status Codes that Apache 2.x was capable of handling. This list contains 83 Status Codes recognized by Apache. I compiled the latest 2.4.4 Apache in order to view the actual codes sent by a live server.. very cool. You can read about the newest HTTP Status Codes in RFC 6585.
This is a big update from the last time I looked into this, when I enumerated 57 Status Codes that Apache 2.x was capable of handling. This list contains 83 Status Codes recognized by Apache. I compiled the latest 2.4.4 Apache in order to view the actual codes sent by a live server.. very cool. You can read about the newest HTTP Status Codes in RFC 6585. Ultimate Redirect Cheatsheet for multiple programming languages. Redirecting Users with Javascript redirect, meta refresh redirect, and php redirect, also htaccess methods, python, coldfusion, asp, perl, etc.
Ultimate Redirect Cheatsheet for multiple programming languages. Redirecting Users with Javascript redirect, meta refresh redirect, and php redirect, also htaccess methods, python, coldfusion, asp, perl, etc.