Magic in the Terminal: Screen, Bash, and SSH
Back in the mid-90's I was doing a lot of war-dialing with modems (a more recent phenomenon is wardriving, the searching for wireless networks (Wi-Fi) from a moving vehicle. Wardriving was named after wardialing, since both techniques involve brute-force searches to find computer networks) and discovering all sorts of networks and machines, many of them were Unix and Solaris based public systems, and when I managed to gain access to the system and found myself staring at a unix shell I was very excited but also a total idiot. In those days of using the phone networks to research unknown systems it was very difficult for anyone to actually get the phone company to trace a call, so instead of what happens today where it is child's play to trace an IP address, back then it was a very real back-and-forth battle between the system admin and whoever was gaining access to their system.
Essentially, I would gain a shell or some kind of terminal, and just go at it trying to figure out what it could do, trying all kinds of commands. Inevitably this would eventually alert even the laziest admin and they would proceed to attempt to lock me out. It was great sport and extremely addictive. When my favorite system (a massive sun machine in the basement of a big library) finally locked me out and I couldn't get back in I went to my local library and got some reading material -- one of my favorites was the red hat bible. I was able to acquire my own computer and the first thing I did was install red hat linux onto it from the discs included with the book. For the next several years I was essentially offline, all we had at home was a modem and it was becoming difficult to locate any more systems in my area code.. I was into phreaking of course as well, but I never was able to make free long-distance war-dialing a reality.
So I just read the books and learned what I could. I would also goto the library when I could in order to use their machines which were connected to the internet (before aol it was much different than today's internet) and since my time was short I would download as many documents as I could so that I could read them offline. The TLDP documentation that we know today was around back then in various forms, and I read every HOWTO in the index, though not understanding half. The other big resource I found for really intense reading was the kernel documentation, which admitedly I still don't comprehend 1/4th of.. I try and peruse all the new documents when a new kernel is released, since the kernel is where all the real action is, hence the military authoritative name, and that is how I discovered one of the coolest features of Linux that I have found. TMPFS!
What I learned
I learned that with our present technology, which I try to keep somewhat updated on, using a mouse to point and click your way to a solution is always much much much slower than just getting dirty and writing straight code to a terminal. BTW, you know they are close (within 100 years) of enabling connection at the speed of thought. Yes it's a mind-meld between you and a super-computer AI to process it. That's the whole story behind popular Japanese anime like "Ghost in the Shell".
That's also a fundamental reason that certain vast segments of the computing world have a dislike of Microsoft, the way they build (to sell) their operating systems.. no open-code, which is their obvious #1 problem, and why they have a million viruses. Perhaps even a bigger issue some have with "the empire", is how they stuck this gooey, thats how you pronounce GUI - graphical user interface, in a way that tries to create multiple classes of people, those behind the scenes with all the control (they are a middleman between you and your real computer, for millions), and a second group of people on the outside, sheep - I believe they are referred to as sheep.
screenrc-exampleCleanup Screenrc Files
You can run this command to get a wildly confusing screenrc file under control. You could have a heavily commented version, and then run this to create the actual... I like to start there but because the screenrc file is read in order, you should take out the 'sort'.
sed -e '/^#/d; s/^[t ]*//g; /^[a-z]/I!d' /etc/screenrc|sort|tr -s ' t' | tr -d '?15?32'
Read lots of .screenrc files
This is easy with Google's futuristic Code Searching Engine! I get excited about this search engine because it is sooo dope! Here's a search for files named .screenrc, thanks for this free tool Google, much love!
Here it is with lots of messy comments still in place.
autodetach on
bufferfile $HOME/.screen/buffer
nethack on # print wackier status messages
chdir $HOME
password HJa4Dp4UIDlLA
setenv LC_CTYPE en_US.UTF-8
sorendition =s Gk
startup_message off
shell bash # use the default shell
shelltitle "$ |bash"
term screen-256color #By default, screen uses an 8-color terminal emulator. Use the following line to enable more colors, more-capable terminal emulator:
defmode 620
defmonitor off # turn monitoring on
defnonblock 5 # flaky/slow ssh lines
defscrollback 300
defutf8 on
hardcopydir ~/.hardcopy/screen_%y-%m-%d_%0c.%n
defbce on # erase background with current bg color
defencoding UTF-8
defflow auto # will force screen to process ^S/^Q
defflow on # disable Ctrl-S/Ctrl-Q "flow control"
defhstatus "screen: ^En (^Et)"
deflogin off
deflog off
logfile ~/.screen/screen_%y-%m-%d_%0c.%n
silencewait 15
vbell_msg " Wuff ---- Wuff!! "
activity "%C -> %n%f %t activity!"
bell "%C -> %n%f %t bell!~"
altscreen on # restore window contents after using (e.g.) vi
attrcolor b ".I" # allow bold colors - necessary for some reason
hardstatus on
hardstatus alwayslastline "[%02c] %`%-w%{=b bw}%n %t%{-}%+w %=%{..Lw} %H %{..g} %m/%d %C%a "
caption always "%{kG}%?%-Lw%?%{bw}%n*%f %t%?(%u)%?%{kG}%?%+Lw%?"
idle 3600 eval "screen nice -n 19 /opt/s/cmatrix" "idle 6400 detach"
msgwait 5 # 1 second messages
multiuser off
nonblock on # If a window goes unresponsive, don't block the whole session waiting for it.
pow_detach_msg "Screen session of $LOGNAME $:cr:$:nl:ended." # emulate .logout message
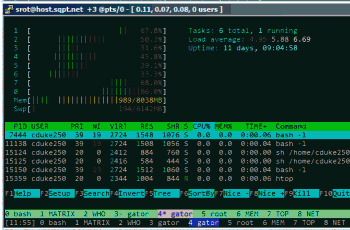
screen -h 500 -t 'bash' sh $HOME/welcome.sh
screen -h 0 -t 'MATRIX' nice -n 19 /opt/s/cmatrix
screen -h 0 -t 'WHO' sudo /opt/s/whowatch
screen -h 100 -t 'gator' sh $HOME/.ssh/start_control.sh
screen -h 100 -t 'gator' ssh gator sh ~/welcome.sh
screen -h 500 -t 'root' sudo bash -l
screen -h 0 -t 'MEM' nice -n 19 sh -c 'sleep 4 && tput civis; CLS=$`tput clear`; trap "tput cnorm; exit 0" 1 2 3; while :; do free -olt && sleep 2 && echo $CLS; done;'
screen -h 0 -t 'TOP' nice -n 19 sh -c 'sleep 4 && tput civis; CLS=$`tput clear`; trap "tput cnorm; exit 0" 1 2 3; while :; do top -b -n 1 -H -d 10 -c |sed "/$USER/!d" && echo $CLS; done;'
screen -h 0 -t 'NET' nice -n 19 sh -c 'while :; do /bin/netstat --numeric-ports -a -e --tcp |sort --key=4 && sleep 5; done;'
select 0
#select -h 100 -t 'log' 4 sudo sh -c 'nice tail -n 60 -s 10 -f /var/log/everything.log | ccze -A'
zombie "^[" # don't kill window after the process died
More on War Dialing
War dialing or wardialing is a technique of using a modem to automatically scan a list of telephone numbers, usually dialing every number in a local area code to search for computers, Bulletin board systems and fax machines. Hackers use the resulting lists for various purposes, hobbyists for exploration, and crackers - hackers that specialize in computer security - for password guessing.
A single wardialing call would involve calling an unknown number, and waiting for one or two rings, since answering computers usually pick up on the first ring. If the phone rings twice, the modem hangs up and tries the next number. If a modem or fax machine answers, the wardialer program makes a note of the number. If a human or answering machine answers, the wardialer program hangs up. Depending on the time of day, wardialing 10,000 numbers in a given area code might annoy dozens or hundreds of people, some who attempt and fail to answer a phone in two rings, and some who succeed, only to hear the wardialing modem's carrier tone and hang up. The repeated incoming calls are especially annoying to businesses that have many consecutively numbered lines in the exchange, such as used with a Centrex telephone system.
The popularity of wardialing in 1980s and 1990s prompted some states to enact legislation prohibiting the use of a device to dial telephone numbers without the intent of communicating with a person.
The name for this technique originated in the 1983 film WarGames. In the film, the protagonist programmed his computer to dial every telephone number in Sunnyvale, California to find other computer systems. 'WarGames Dialer' programs became common on bulletin board systems of the time, with file names often truncated to wardial.exe and the like due to length restrictions on such systems. Eventually, the etymology of the name fell behind as "war dialing" gained its own currency within computing culture.[1]
A more recent phenomenon is wardriving, the searching for wireless networks (Wi-Fi) from a moving vehicle. Wardriving was named after wardialing, since both techniques involve brute-force searches to find computer networks. The aim of wardriving is to collect information about wireless access points (not to be confused with piggybacking).
Similar to war dialing is a port scan under TCP/IP, which "dials" every TCP port of every IP address to find out what services are available. Unlike wardialing, however, a port scan will generally not disturb a human being when it tries an IP address, regardless of whether there is a computer responding on that address or not. Related to wardriving is warchalking, the practice of drawing chalk symbols in public places to advertise the availability of wireless networks. Despite its widespread coverage [in the news?], warchalking never particularly caught on as a popular activity.
The term is also used today by analogy for various sorts of exhaustive brute force attack against an authentication mechanism, such as a password. While a dictionary attack might involve trying each word in a dictionary as the password, "wardialing the password" would involve trying every possible password. Password protection systems are usually designed to make this impractical, by making the process slow and/or locking out an account for minutes or hours after some low number of wrong password entries.
War dialing is sometimes used as a synonym for demon dialing, a related technique which also involves automating a computer modem in order to repeatedly place telephone calls.
This page contains content from article and is released under the CC-BY-SA.
« Securing php.ini and php.cgi with .htaccessDealing with Mobile Visitors using Bad Browsers »
Comments