Fsockopen Magic
 PHP's fsockopen function lets you open an Internet or Unix domain socket connection for connecting to a resource, and is one of the most powerful functions available in the php language.
PHP's fsockopen function lets you open an Internet or Unix domain socket connection for connecting to a resource, and is one of the most powerful functions available in the php language.
PHP fsockopen for FAST DNS lookups over UDP
While reading up on gethostbyaddr on PHP.net, I saw a nice idea for using fsockopen to connect over UDP port 53 to any Public DNS server, like Google DNS 8.8.8.8, and sending the reverse addr lookup in oh about 100 bytes, then getting the response in oh about 150 bytes! All in less than a second. This is how/why to read/write data directly to the wire! This would be extremely valuable for use in things like my online header tool because it's faster than any other method. As usual, I went a bit overboard optimizing it to be lean and fast.
Faster Form Submission and Processing with fsockopen
 Part II: Example illustrating how to speed up GET/POST form submissions. Uses fsockopen to initiate a server-side background request to process the submitted data, so that the result page of the form is displayed to the client lightningly quick.
Part II: Example illustrating how to speed up GET/POST form submissions. Uses fsockopen to initiate a server-side background request to process the submitted data, so that the result page of the form is displayed to the client lightningly quick.
Faster POST and GET Form Submissions… Shazam
 Just a very brief look at speeding up form submission by delegating the processing and bandwidth to your server, not your client.
Just a very brief look at speeding up form submission by delegating the processing and bandwidth to your server, not your client.
Password Protection Plugin Status
Enumerating Permissions can be Annoying
Don’t ask me how because I won’t tell you, but on one of the hosts I was testing on that did not allow direct access I was able to get the Apache server running as dhapache to erroneously write a file into my users blog directory. This is a big security no-no and I now have my .htaccess file written into the blog directory where it should go, but instead of my php script’s user having write access to the file so I can modify it, its owned by dhapache! Because the file is owned by dhapache I shouldn’t even be allowed to know it exists, but there it is. So the next step was to try and take ownership of the .htaccess file so that I could modify it. I tried and tried but was unsuccessful, I couldn’t modify it so that was another dead end. Actually it took me awhile to figure out how to remove the file from my directory. Being that it was owned by dhapache I couldn’t delete or modify it using my php process or even through ftp/ssh! Sysadmins regularly run find commands that search the servers for any files owned by dhapache that should not be there as this is a big red flag that someone has found a way to manipulate dhapache which could potentially lead to modifying dhapache-owned server config files, which sometimes is all it takes to hack your website and server.. Luckily I was able to delete it by basically running the hack again to overwrite the file.
An AskApache Plugin Upgrade to Rule them All
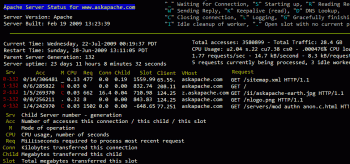 So my blog as been rather quiet for almost a year now, and very few updates if any have been released for my Password Protection PLugin, my Google 404 Plugin, and definately not for my AskApache CrazyCache plugin, which I will be releasing last... So for all of you who've helped me out by sending me suggestions and notifying me of errors and sticking with it... Just wanted to say sorry about that, and thanks for all the great ideas.. Well, I've been sticking with it as well believe it our not. I manage to get free days once in a while, and then its time to jam.
So my blog as been rather quiet for almost a year now, and very few updates if any have been released for my Password Protection PLugin, my Google 404 Plugin, and definately not for my AskApache CrazyCache plugin, which I will be releasing last... So for all of you who've helped me out by sending me suggestions and notifying me of errors and sticking with it... Just wanted to say sorry about that, and thanks for all the great ideas.. Well, I've been sticking with it as well believe it our not. I manage to get free days once in a while, and then its time to jam.
Htaccess SetEnvIf and SetEnvIfNoCase Examples
SetEnv, SetEnvIf, and SetEnvIfNoCase directives conditionally set environment variables accessible by scripts and apache based on HTTP Headers, Variables, and Request information.
Crazy Cache WordPress Plugin Released
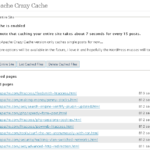 A WordPress plugin that caches your entire blog for WP-Cache, I love this plugin and finally released it to the public!
A WordPress plugin that caches your entire blog for WP-Cache, I love this plugin and finally released it to the public!
Chmod, Umask, Stat, Fileperms, and File Permissions
Unix file permissions are one of the more difficult subjects to grasp.. Well, ok maybe "grasp" isn't the word.. Master is the right word.. Unix file permissions is a hard topic to fully master, mainly I think because there aren't many instances when a computer user encounters them seriously, and bitwise is oldschool. This contains a listing of all possible permission masks and bits from a linux, php, and web hosting view.... cuz you guys AskApache Regs Rock!